What Is an API Endpoint and Why Is It Important?
An API platform helps empower the IT world. Almost every organization adopts API strategies to deliver an incredible user experience and enhance business growth. API facilitates the data required for providing solutions to user problems. However, you must understand what APIs are, how they work, and the functionality they bring to your application or website before implementing them into the system. An API endpoint is a single end of a communication channel that enables sharing of application data and information.
What Is an API Endpoint?
An API endpoint acts as a touchpoint between an API and a server. API endpoints are the means through which APIs can access resources required from a server to perform specific tasks. Developers implement the endpoints as communication channels to make their requests related to api documentation. API endpoint acts as a digital location where the API receives requests about resources on the server. The endpoint is a uniform resource locator (URL) for APIs that provides the resource location of a server. APIs work with two channels – requests and responses. When any API requests information from a web server or application, it receives a response from the server. The location where APIs send requests for resources and their location is the API endpoint.
Endpoint vs API
APIs and endpoints are not the same things. The endpoint is an API component and is a set of rules allowing two applications to share their resources. Endpoints are the locations of the resources, and APIs use the endpoint URLs to retrieve them. API refers to a set of tools or protocols that allows interaction between applications for easy deployment. The technique enables third-party vendors to write programs that interface with each other. On the other hand, an endpoint is a location where applications interact with each other. So, API is the system of protocols that allows communication between systems. But an endpoint is a URL that enables APIs to access resources within a server.
How Do API Endpoints Work?
When two software applications integrate over a network or the internet, an application acts as the client and sends a request to another application’s API. A resource request from the app’s database may get sent depending on API capabilities. The client may also ask the app to perform actions on the server. The API performs the requested action after receiving and verifying the client’s request and sends a response. The response includes the resources requested by the client.
APIs allow access to multiple resources like content, media, authors, etc. However, the process leaves clients in a dilemma about specifying which resource they want to access in their server request. This is where end to end api management comes in handy. The system helps clients identify an API endpoint call in the form of a URL in their request system. Their requests inform the server about the resource they want from a specific location.
So, API endpoint documentation provides a means of interaction between a server and an API. Each endpoint offers a specified format for the request and the responses. The best part about API endpoints is that you do not need prior knowledge to use the system.
However, you must monitor and secure API endpoints to ensure you find the issues to resolve them before the users experience them. Given below is a breakdown of how you can secure API endpoints.
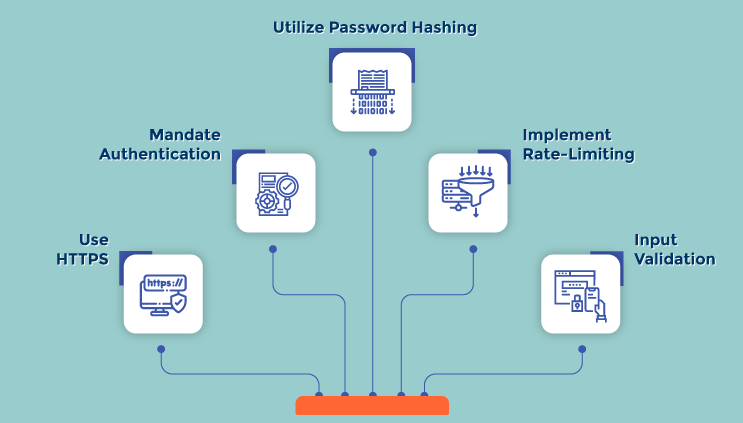
Utilize Password Hashing
You can store passwords using asymmetric encryption algorithms to guarantee the safety of API endpoints. You should avoid plain-text and symmetric storage of passwords to prevent advanced security breaches in the system.
Use HTTPS
APIs that allow applications or users to interact via HTTP and other non-secure protocols are prone to hackers and intruders. So, you can use HTTPS as the only option for system interactions to avoid putting your clients in danger.\
Implement Rate-Limiting
You can enforce limits on the number of requests a user can make to the API to discourage hackers and bots and avoid the wastage of system resources. You can include rate-limiting norms during the API endpoint testing to avoid last-minute errors or discrepancies.
Mandate Authentication
Although APIs have distinct authentication forms, you can ensure add-on security by mandating other authentication techniques to segregate accounts into various resources and limit permits to token bearers.
Input Validation
If you validate inputs, it helps you to identify or decipher threats early before reaching the clients. You must check for errors, discrepancies, etc., to ensure the data is in the correct format to prevent erasing it from the database.
API Endpoint and Why You Need One?
Organizations leverage APIs to transfer information, transactions, processes, etc. So, API usage has increased with time because it enables organizations to allow third-party developers to create applications that improve the usage and adoption of system platforms. The process helps businesses build an ecosystem dependent on the data derived from APIs that leads to additional revenue opportunities.
api gateway accommodates access to the server and client communication. APIs will remain confusing and broken without proper functioning and structured endpoints. Organizations must ensure that an API endpoint provides valuable resources for clients to make the relevant data available via API platforms.
API endpoint specifies where you can access the resources from the APIs and plays a significant role in guaranteeing the correct functioning of the software in interaction. An API’s performance depends on the ability to communicate via the API endpoint.
Summing It Up
The API endpoint is the system where APIs receive requests about a resource on the server. The endpoint acts as a URL to provide the resources on the specific server. So, the endpoint acts as a communication channel between a server and an API.
If you are looking for a Unified API Platform to implement on your system, Unified.cc is your answer. The platform allows you to connect multiple APIs via a single API without connector-specific variations. Unified.cc also eliminates the need to maintain multiple copies of a code and speeds up the development time to allow the team members to focus on other relevant tasks.
Know Why Unified.cc is Best for Unified API Platform?
Join the SaaS Revolution
-
All-in-One Suite of 50 apps
-
Unbelievable pricing - â¹999/user
-
24/5 Chat, Phone and Email Support
Infinity Suite
Tags
Email Finder Author Finder Email Validator Email List Email Hunter Email Checker Email Lookup Email Extractor Email Address Finder Email Scraper Find Emails CRM Software CRM Sales CRM CRM Software Enterprise CRM Software Cloud CRM Software Sales Enablement Workflow Automation Retail CRM Call Center CRM Real Estate CRM Sales Tool SDR Software Sales Engagement Platform Sales Qualified Leads Lead Management Tool Sales Tracking Sales Automation Outbound Sales Sales Prospecting Follow Up Leads Lead Management Call Center Software Call Center Software Outbound Call Center Auto Dialer Software Dialer Call Monitoring Automatic Call Distributor Answering Machine Detection Cloud Contact Center Software Virtual Call Center Call Management Time Tracking Time Tracking Employee Monitoring Time Tracker Time Tracking Software Timesheet Employee Time Clock Employee Tracking App Timekeeping Tracking App Time Clock App Applicant Tracking System ATS Applicant Tracking System Application Tracking System Applicant Software Recruiting Software ATS System Applicant Tracking Applicant Tracker Recruitment Software Candidate Relationship Management Systems Video Interviews Assessment Management Recruitment Software Video Interview Virtual Interview Coding Interview Interview Tool Online Assessment Employment Assessment Test Position Management Hiring App HRMS Software Human Resource Management HRMS Software HR Software Payroll Software Human Resource Software Employee Onboarding HRMS HR System Employee Management Document Management AI Writer Lead Enrichment AI Email Writer Sales Pitch Writer AI LinkedIn Outreach SEO Email writer Backlink Email Writer LinkedIn Chrome Extension Opening Line Writer Lead Generation Linkedin Search Prospect Lead Generation Sales Generation Data Enrichment CRM Integrations Technology Search Search with Email Integrations Website Search OKR Tool KPI OKR Task Management Performance Review Employee Performance Evaluation Employee Review Performance Management System OKR Goals MBO Email Notifications Learning Management System LMS Elearning Enterprise Learning Management Professional Development Employee Training Learning Management System Learning Platform Asynchronous Learning Training Management Knowledge Management Chatbot Chatbot AI Chatbot Customer Service Chatbot Online Chatbot Create Chatbot Messenger Chatbot Chatbot Software Website Chatbot Software Survey Bot Bot Builder Help Desk Software Ticketing Tool User Experience Help Desk Software Ticketing System Helpdesk Ticketing System Feedback Management Service Desk Software Support Ticketing Software Helpdesk Support Software Customer Service Ticketing System Live Chat Customer Service Software Live Chat Software Live Chat App Live Chat System Website Live Chat Live Chat Tool Web Chat Software Live Chat Support Software Customer Service Tool Live Chat Service Customer Feedback Customer Feedback Survey Customer Feedback Management Software Feedback Management Tool Customer Satisfaction Survey Software Customer Feedback Management System Client Feedback Software Survey Analysis Feedback Survey Software Feedback Management System User Feedback Software Customer Onboarding Customer Success Management Onboarding Process Workflows Customer Retention Customer Journey Onboarding Checklist User Segmentation Personalization Customized Templates Popup Builder API Platform End To End API Management Unified API Control REST API Management Web API Gateway API Documentation API Management API Integration API Development Unlimited Projects API Gateway Single Sign on Authentication Software Application Management Password Management SSO Configuration SSO Single Sign-On Access Management Easy Set-Up Single Login Secure Login App Builder App Builder Platform Low Code Application Platforms Low Code Development Build Your Own App Low Code App Software Drag And Drop Builder Custom Application Low Code Platform Low Code No Code Bespoke Software App Widgets Custom Widget File Picker Playground OAuth Keys File Manager Website Monitoring Reporting Web Application Monitoring Website Monitoring App Monitoring Performance Monitor App Baseline Analysis Location Insights Alerting System Reporting Wireframe Tool Design UI UX Project Management Mock Designer Wireframe Designer Website Mockup UI Prototyping Image Library Project Management Real-Time Updates Design UI UX Website Builder Website Builder Webpage Builder Website Creator Landing Page Creator Website Maker Blog Builder Ecommerce Website Builder Website Analytics Website Development Landing Page Builder Email Marketing Email Marketing Software Bulk Email Sender Automated Email Email Campaign Systems Email Automation Software Autoresponders Email Blast Service Email Marketing Email Marketing Automation Drip Campaigns Social Media Management Instagram Post Scheduler Social Media Analytics Social Media Management Social Media Planner Social Media Calendar Social Media Scheduling Social Media Listening Social Media Monitoring Social Listening SEO Tool Keyword Tool Link Building SEO Optimizer Website Audit On-Page SEO Broken Link Checker Rank Tracker Website Grader SEO Competitor Analysis Website Recording Website Analytics Click Tracking Usability Testing Website Monitoring Mouse Tracking Visitor Recording Session Replay Conversion Funnels Website Recording Website Visitor Tracker Website Personalization Lead Generation Tool Popup Maker Lead Generation Software Popup Builder Website Personalization Software Lead Capture Software Popup Builder Lead Capture Tool Lead Generation App Website Personalization App Content Planner Content Planner AI Writer Social Media Content Planner Ai Content Writer Social Media Content Calendar Content Generator AI Blog Writer Content Marketing Software Social Media Calendar Social Media Planner Push Notification Push Notification Push Messages Push Notification Service Push Service Push Notification App Custom Notifications Mobile Push Notifications Push Notification For Website Push Notification Tool Push Notification Providers Image Personalization Email Marketing Template Countdown Clock Personalization Software Personalized Software Countdown Clock Countdown Timer In Email Personalization Tool Personalized Images Personalized Videos Conversational Chatbot PPC Management Keyword Research PPC Management PPC Marketing Keyword Finder Keyword Generator Shopping Ads Adwords Reports Keyword Research Tool Keyword Suggestion Tool Team Chat Team Chat Software Collaboration Software Team Collaboration Team Communication Online Collaboration Collaboration Tool Teamwork Collaboration Virtual Communication Team Collaboration Software Business Phone System Virtual Phone Numbers Virtual PBX Toll Free Numbers Business Phone System IVR PBX Small Business Phone System PBX System VoIP Phone Cloud Phone Video Conferencing Video Conferencing Video Call Recording Virtual Conferencing Software Virtual Meetings Virtual Meeting Platforms Virtual Conference Platforms Online Conference Platforms Video Calling Software Cloud Meetings Video Conferencing Software Email Provider Email Software Software For Emails Hosted Emails Email With Domain Custom Email Address Email Hosting Business Email Address Email Encrypted Custom Domain Email Project Management Software Project Management Task Management Project Planner Project Management Tool Task Management Software Project Planning Software Project Management App Task Management App Project Management System Project Management Software Form Builder Form Builder Survey Builder Order Forms Web Forms Form Maker Form Creator Form Designer Survey Maker Survey Creator Custom Form Appointment Scheduling Appointment Scheduling Software Appointment Scheduling System Meetings Scheduler Appointment Scheduling App Online Appointment Scheduling Online Scheduling App Appointment Scheduler Appointment Booking App Calendar Scheduler Online Scheduler Robotic Process Automation RPA Tools RPA RPA Automation Robotic Automation Software Data Scraper Web Scraper Robotic Automation Website Scraper Business Process Automation Robotic Process Automation Business Process Management Workflow Management Business Process Modelling Business Process Automation BPMN BPM Software BPM Tool Business Process Management Workflow Software Workflow Automation Business Process Mapping App Integration Workflow Software Workflow App Workflow Automation Process Automation Application Integration Data Integration Tool Workflow Management Software Data Integration Software Workflow Tool Marketing Automation Electronic Signature Signature Maker Digital Signature Software Digital Signature Pdf Signer Esign Online Signature Signature Creator Sign Documents Online Electronic Sign E Signature
