Best Practices for API Security
As APIs become more and more ubiquitous, it’s important to have best practices in place to ensure that your data is safe.
#1
Minimal Coding
#2
Lower Maintenance Cost
#3
Automated Software
#4
Advanced Security
#5
Multi - APIs Connectivity
#6
Data Privacy
#7
Performance Tracking & Monitoring Tool
#8
Centralized Logging System
#9
Unbelievable pricing - the lowest you will ever find
#10
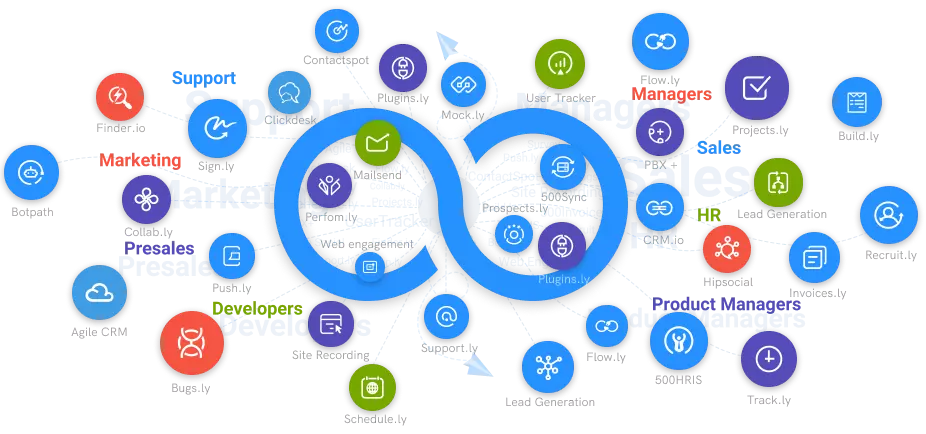
Everything your business needs - 50 apps, 24/5 support and 99.95% uptime
API Security Best Practices
If enterprises plan to offer their APIs publicly, it is vital that they follow certain fundamental security best practices and use well-established security measures.
Determine your weaknesses
Knowing which stages of the API lifecycle are unsafe is the only way to safeguard APIs successfully. This may not be that easy to do, especially as the organization's usage of APIs grows. APIs must be regarded as software artifacts on their own and must follow a complete lifespan, including maintenance and retirement. It is essential to evaluate the entire API lifecycle in end to end api management.
Make use of a solid authentication and authorization solutions
Many publicly available APIs suffer from non-existent or poor authorization and authentication. In fact, hackers can easily attack your APIs when you do not enforce authentication or when an authentication factor is readily broken into. As APIs give access to an organization's databases, it is vital that access to them is properly controlled. You must use solutions based on robust, established authentication and authorization technologies wherever possible.
Tokens should be used
Token usage is a good API security practice in general. Tokens granted to identities can be used by developers as a reasonably simple method to control access to services and establish trusted identities.
Make use of a service mesh
Service mesh technology, like API gateways, adds another layer of control as it sends requests from one service to the other. A service mesh optimizes how all of these moving pieces interact, including the implementation of correct authentication, access control, and other security mechanisms. API administration is shifting to the service communication layer. Thus, solutions are accessible at the service mesh layer. If the APIs have easy deployment then the number of APIs grows, automation and security become increasingly important.
Create a threat model
Threat modeling is a methodical way to identify and assess threats. Threat models are most effective when utilized as a preventative strategy, but they should also be viewed as a continuous cycle for analyzing, mitigating, and preventing application vulnerabilities in an automated yet regulated manner.
Don't reveal any more information than is absolutely essential
Some APIs give way too much information, whether it's the amount of unnecessary data returned by the API or information revealing far too much about the API endpoint. This usually happens when an API delegates the responsibility of filtering data to the user interface rather than the endpoint. You must ensure that APIs only return the information required for employees to perform their job. Furthermore, at the API level, you can impose data access limits, monitor data, and obfuscate if the return contains confidential data.